SSH a practical guide
Wed Nov 26 2025 00:00:00 GMT+0000 (Coordinated Universal Time)
Remote management tool that gives access to run commands on another machine. The SSH client installed on your PC won’t let others connect to your PC from outside.
which ssh
apt search openssh-client
ssh root@172.105.7.26
# to disconnect
ctrl+DOn the server, you can see the log file for connections and which clients are connected now:
tail -f auth.log
OpenSSH Client Configuration
cd ~/.ssh
touch config
# put the following lines inside that
Host myserver
Hostname 192.233.2.23
Port 22
User root
# then execute in a single line
ssh myserver
# run the last ssh command
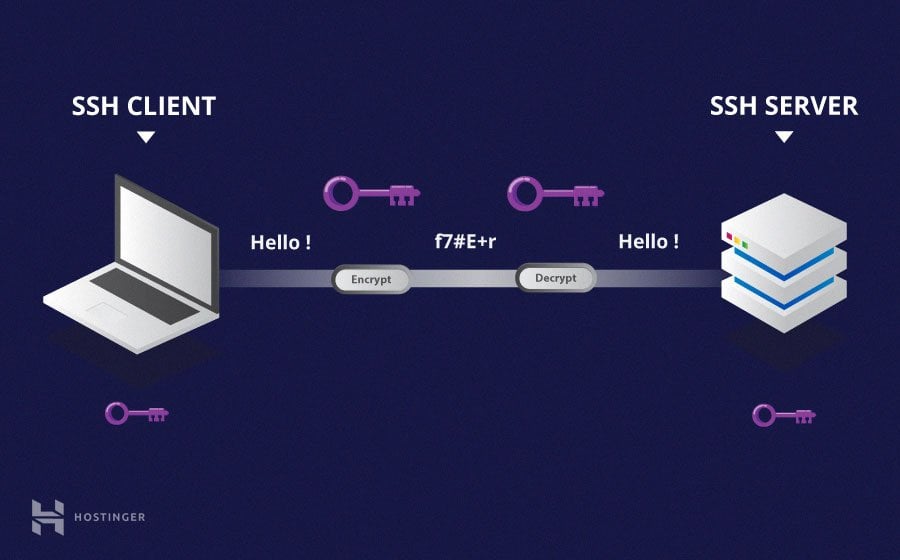
!sshPublic and Private Key
Issues with password authentication: Brute force, requires entering password every time. Passwords are not that secure, so create a key.
First, look at what is inside the key folder, then execute ssh_keygen, give a passphrase to avoid anyone else using the key. Key ending with .pub is the public key. Copy the public key to the server:
mkdir .ssh
cd .ssh
nano authorized_keys
# paste your public key here
# another easy way
ssh-copy-id -i ~/.ssh/id_rsa.pub root@192.234.2.26Managing Keys
When you have access to many servers, using one public key is not safe because one breach affects everything. Also, SSH will search through all keys, which can sometimes create a timeout.
ssh-keygen -t ed25519 -C “acme”
this encryption is better than RSA
Naming convention: .ssh/acme_id_ed25519
Keep the private key alive with the agent:
eval "$(ssh-agent)"
ps aux | grep ssh-agentAdd keys to ssh-agent:
ssh-add ~/.ssh/acme_ed25519
This helps avoid entering the passphrase every time after Linux boot.
Server Configuration
sshd is the server daemon that runs in the background to accept connections. systemctl stop sshd will not disconnect active devices, but after they finish, no one can access the server.
cd /etc/ssh
ssh_config -> global client config
sshd_config -> server configuration
# after changing the file, restart
systemctl restart sshdDo not close the terminal when restarting; open another terminal to check. Take backups to avoid malicious activity:
mv .ssh .ssh-bak
rm -r .ssh
mv .ssh-bak/ .sshTroubleshoot SSH:
journal -fu ssh
Agent Key Forwarding
Great reading material: SSH Agent Forwarding
Ordinary password authentication
Simple to setup, usually default, easy to understand, reduces admin burden. Cons: Brute force attacks, requires password entry every time.
Public key access
Public key: long string of bits encoded in ASCII.
Type + key + comment.
Possible to have the same passphrase for all keys, but tedious to type like password auth.
Agent
Supports subsequent connection requests.
Without agent, scripted updates require multiple password prompts.
Public key access with agent forwarding
Allows chaining SSH connections to forward key challenges back to the original system, avoiding passwords on intermediate machines.
Key challenge: creates a large random number encrypted with the user’s public key. ps can show running SSH processes, netstat points to your home system.
NOTE: Agent forwarding cannot fully protect against a root user hijacking the SSH agent socket. Disable if the remote system cannot be trusted.
Testing
Usually, we SSH a Raspberry Pi or similar from our computer. Using a VM to clone the same Linux environment is useful:
Clone one VM
Set Network option -> Bridged adapter -> random MAC address
Install SSH server:
sudo apt install openssh-server
Sometimes having a hostname is not useful for day-to-day work, so change it:
sudo hostnamectl set-hostname <newhostname>
Before installing Guest Additions in the VM, perform these initial tasks:
sudo apt update
sudo apt install
sudo apt-get install build-essential
sudo apt-get install make